Multi-Factor
Authentication (MFA)
Untouchable time to value
100% cloud-based back end, simplifies implementation and accelerates time to value for organisations of all sizes.
Frictionless user experience
Adaptive multi-factor authentication delivers a friction-less user experience - intelligently challenging users only when risk is high.
Ease of deployment
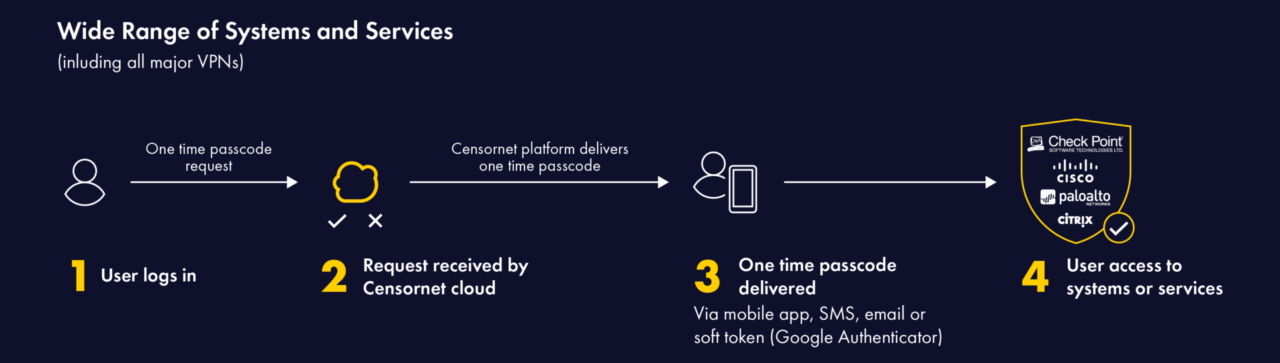
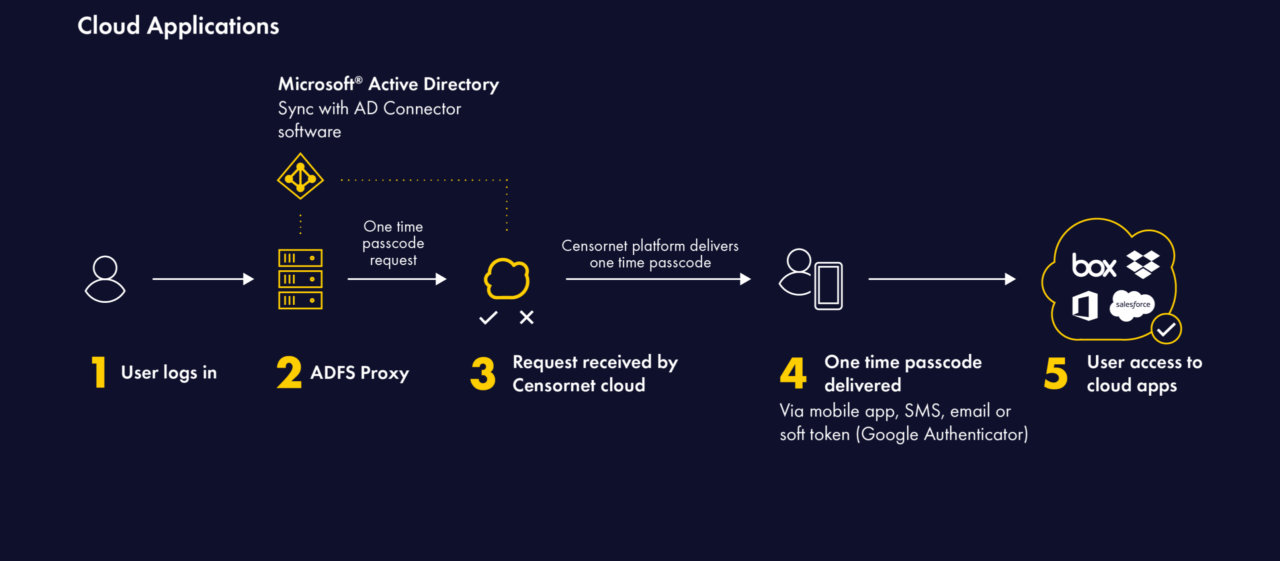
Out-of-the-box support for a wide range of systems, services and applications including all major VPN vendors and cloud applications.
 + combine with other security products to unlock the benefits of ASE
+ combine with other security products to unlock the benefits of ASE
Enable traditionally silo’d products to share and react to security events and state data whilst leveraging world class threat intelligence. Prevent attacks before they enter the kill chain.
Intelligent, adaptive MFA solution
Passwords are not enough. Multi-Factor Authentication adds an additional layer of protection to user and privileged accounts – eliminating account compromise and identity related threats.
 Dangerous content
Dangerous content
Over 81% of data breaches start with a weak or stolen credential.
 Insecure OTP delivery
Insecure OTP delivery
Some OTPs sent by legacy solutions are susceptible to interception and vulnerable to phishing and MITM attacks.
 Insider threat
Insider threat
How Censornet Multi Factor Authentication works
Add an additional level of protection to user accounts above and beyond a simple password. Prevent unauthorised access in the event of password phishing, theft or brute force attack.
Features & Benefits of Multi Factor Authentication
 Real-time session-specific One-Time Passcodes (OTPs)
Real-time session-specific One-Time Passcodes (OTPs)
 Wide Application Support
Wide Application Support
 Automatic Delivery Failover
Automatic Delivery Failover
 Integrated with AD
Integrated with AD
 Ease of Deployment
Ease of Deployment
 User Experience
User Experience
Intuitive user interface
Interested in finding out more?
Multi-Factor Authentication Clients















What Our Customers Say
Our platform
Total visibility, seamless authentication and powerful intelligence.
All at your fingertips with integrated email, web and cloud security with identity and context.





 Pioneering ASE technology
Pioneering ASE technology